The latest news from California
Provided by AGPBG Titan Group 2026 Report Urges Shift From Reactive Security to Denial-of-Opportunity in Critical Infrastructure
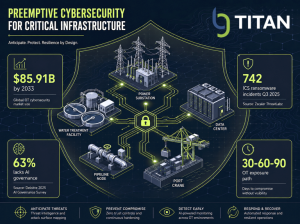
BG Titan Group's preemptive cybersecurity model wraps critical infrastructure assets in a single protective shield, anticipating threats across a global OT cybersecurity market projected to reach $85.91 billion by 2033.
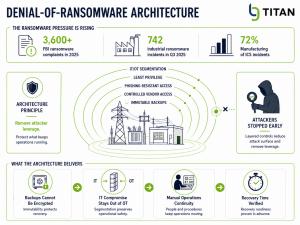
Concentric layers of defense, from IT/OT segmentation to immutable backups, remove the leverage that makes ransomware profitable, with FBI complaints surpassing 3,600 in 2025 and 72% of ICS incidents hitting manufacturing.
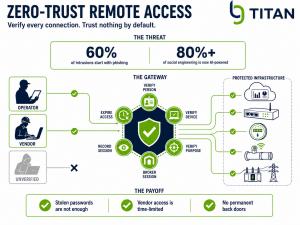
A central verification gateway approves, monitors, and revokes every remote session, so stolen passwords alone cannot reach the systems that run critical infrastructure, an essential defense when AI-powered social engineering now exceeds 80% of attempts.
31-page report maps twelve resilience plays for operators facing an $85.91 billion critical infrastructure protection market by 2033.
SAN DIEGO, CA, UNITED STATES, May 13, 2026 /EINPresswire.com/ -- As ransomware complaints to the FBI surpass 3,600 in a single year, as state-linked actors pre-position inside utility networks, and as AI-supported phishing now accounts for more than 80% of observed social engineering activity worldwide, BG Titan Group has released its 2026 Preemptive Cyber Defense for Critical Infrastructure report, a 31-page strategic document arguing that the cybersecurity conversation in power, water, transport, telecom, and industrial operations must move from reactive recovery to denial-of-opportunity.
The thesis is simple and uncomfortable. Most critical infrastructure operators are still buying cybersecurity as an IT add-on after construction, after procurement, after commissioning, and often after a breach. The new market reality, the report argues, is that cybersecurity must be designed into the asset itself: physically strong, digitally resilient, operationally recoverable, AI-aware, and safe under stress.
A Market Moving From Response Spending to Resilience Investment
The numbers behind the shift are substantial. According to Grand View Research, the global cybersecurity market for critical infrastructure protection was estimated at approximately USD 56.52 billion in 2025 and is projected to reach approximately USD 85.91 billion by 2033. The broader critical infrastructure protection market was estimated at approximately USD 151.00 billion in 2025 and is projected to reach approximately USD 229.12 billion by 2033, driven by digitalization, IT and OT interconnectivity, mega-infrastructure projects, cyber insurance adoption, and board-level focus on operational resilience.
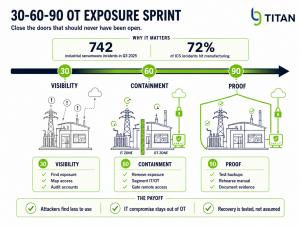
Demand is not theoretical. The FBI’s 2025 IC3 report identified 63 new ransomware variants in a single year, with reported losses exceeding USD 32 million, and noted that figure undercounts true costs such as downtime, lost wages, equipment, and third-party remediation. Dragos identified 742 ransomware incidents affecting industrial entities worldwide in the third quarter of 2025 alone, with manufacturing accounting for 72%.
“The era of treating cybersecurity as a software purchase is over,” the report states. “For critical infrastructure, the question is whether the asset can be safely operated, updated, monitored, and recovered for its entire lifecycle. That is no longer a vendor decision. It is a design decision.”
Four Forces Reshaping the Threat Surface
The report identifies four converging forces redrawing the cyber risk map for infrastructure owners.
The first is the collapse of the perimeter. Plants, pipelines, substations, water systems, and ports were once protected by physical isolation. Today they are connected through remote access, sensors, cloud dashboards, contractors, smart meters, edge devices, vendor portals, and AI tools. CISA, the FBI, the EPA, and the DOE now jointly recommend that operators remove operational technology connections from the public internet, change default passwords, secure remote access, segment IT and OT networks, and maintain the ability to operate manually.
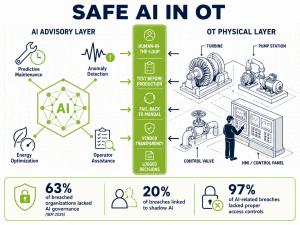
The second is the AI inversion. The UK National Cyber Security Centre assesses that AI will almost certainly continue to make cyber intrusion operations more effective and efficient through 2027, increasing both the frequency and intensity of cyber threats. IBM’s 2025 breach research found that 63% of breached organizations lacked AI governance policies, that 20% experienced breaches linked to shadow AI, and that 97% of organizations reporting AI-related breaches lacked proper access controls.
The third is supply chain pressure. The EU Cyber Resilience Act introduces mandatory cybersecurity requirements for manufacturers of products with digital elements, with reporting obligations applying from September 11, 2026, and main obligations from December 11, 2027. Combined with the EU NIS2 Directive, which establishes a unified cybersecurity framework across 18 critical sectors, the regulatory direction is clear: evidence is replacing assurance, and weak supplier hygiene is becoming a transaction risk that affects financing, insurance, valuation, and government approvals.
The fourth is convergence. A cyberattack on scheduling systems can become a port disruption. A telecom outage can cascade into emergency services, payments, transport, and operations. CISA, the NSA, and the FBI have assessed that PRC state-sponsored cyber actors sought to pre-position on IT networks for disruptive attacks against U.S. critical infrastructure in the event of a major crisis. The boardroom and the control room now share the same risk.
Twelve Opportunities and a 30-60-90 Path
The BG Titan report maps twelve concrete opportunity areas where the shift from reaction to denial-of-opportunity creates near-term value. They include cyber-resilient EPC and PMC project delivery, OT exposure reduction sprints, controlled remote operations and zero-trust edge access, AI threat readiness and shadow-AI control, safe AI-in-OT integration, denial-of-ransomware architecture, supplier trust and secure procurement, secure edge infrastructure, compliance-to-resilience programs, integrated cyber-physical resilience design, cyber due diligence for infrastructure deals, and managed OT resilience and training.
For operators looking to act fast, the report introduces a 30-60-90 OT exposure reduction path. In the first 30 days, identify internet-facing OT, remote access paths, exposed engineering tools, shared accounts, default credentials, and critical supplier connections. In the next 60 days, remove public exposure, disable unnecessary services, enforce phishing-resistant access where possible, close dormant accounts, place remote access behind controlled gateways, and separate IT from OT pathways. In the final 30 days, document the new access model, validate segmentation, confirm backup and manual operation plans, review supplier access logs, and rehearse incident escalation.
“The first cyber win for most operators is not advanced AI,” the report observes. “It is closing the doors that should never have been open in the first place.”
Ten Questions for Boards, Ministries, and Operators
The report closes with a decision agenda rather than a technical checklist. Among the ten questions every critical infrastructure customer should be able to answer now: What operational systems are reachable from the internet? Which vendors can remotely access our environment? Can IT compromise reach OT? Are default credentials fully removed? Can we operate manually if digital systems are degraded? Have we restored from backups recently? Where are AI tools touching our data or operations? Do executives know who decides during a cyber incident? Can we prove our resilience to regulators, lenders, insurers, and customers?
Unanswered questions, the report argues, should become funded workstreams.
Risk Factors and Direction of Travel
BG Titan flags several risk factors operators must price into investment decisions. Regulatory timelines are accelerating, with NIS2 transposition obligations and the Cyber Resilience Act both moving toward full enforcement. AI integration into OT can introduce new vulnerabilities, including process-model drift and safety-process bypasses, particularly when vendor transparency is limited. Insurance and capital markets are tightening their cyber diligence expectations, and the cost of remediation rises sharply once weak equipment is purchased, installed, integrated, and commissioned.
The direction of travel, however, is unambiguous. Critical infrastructure will be either resilient by design or exposed by default. The organizations that move first will not simply reduce cyber risk. They will protect uptime, safety, capital, reputation, compliance, and public trust.
About BG Titan Group
BG Titan Group is a multi-jurisdiction holding structure with subsidiaries spanning infrastructure, natural resources, energy and power, financial services, technology, media and telecommunications, and water services, operating across the United States, UAE, East Africa, Europe, and additional jurisdictions. The group provides EPC, PMC and PMT, procurement, project development, financing advisory, risk control, and customer-specific IT and cybersecurity solutions, deploying an asset-light sovereign deal origination model across infrastructure, energy, agriculture, technology, and trade.
Jamila Hasanova
BG TITAN GROUP
+1 332-301-4222
email us here
Legal Disclaimer:
EIN Presswire provides this news content "as is" without warranty of any kind. We do not accept any responsibility or liability for the accuracy, content, images, videos, licenses, completeness, legality, or reliability of the information contained in this article. If you have any complaints or copyright issues related to this article, kindly contact the author above.